2 days ago ssh woes with openSSH in windows. Setting up OpenSSH for Windows using public key authentication. How to set GSSAPIAuthentication and GSSAPIDelegateCredentials attributes through CPAN module Net-OpenSSH. How to connect to WIndows node using openSSH and Ansible? 14.11 OpenSSH Contributed by Chern Lee. OpenSSH is a set of network connectivity tools used to access remote machines securely. It can be used as a direct replacement for rlogin, rsh, rcp, and telnet.Additionally, TCP/IP connections can be tunneled/forwarded securely through SSH. See full list on docs.microsoft.com.

SSH (Secure SHell) is an encrypted terminal program that replaces the classic telnet tool on Unix-like operating systems.
In addition to remote terminal access provided by the main ssh binary, the SSH suite of programs has grown to include other tools such as scp (Secure Copy Program) and sftp (Secure File Transfer Protocol).
Originally, SSH was not free. However, today the most popular and de-facto standard implementation of SSH is OpenBSD's OpenSSH, which comes pre-installed on Gentoo.
Installation
Check install
Most deployments of Gentoo Linux will already have OpenSSH installed on the system. This can be checked by running the ssh command. If it is installed a usage statement should be printed:
If no usage statement is printed ssh is either corrupted or not installed. It is also possible that a user is simply rebuilding OpenSSH to include a new USE configuration. Whatever the case, proceed on to view possible USE settings.
USE flags
USE flags fornet-misc/opensshPort of OpenBSD's free SSH release
X | Add support for X11 |
X509 | Adds support for X.509 certificate authentication |
audit | Enable support for Linux audit subsystem using sys-process/audit |
bindist | Disable EC/RC5 algorithms in OpenSSL for patent reasons. |
debug | Enable extra debug codepaths, like asserts and extra output. If you want to get meaningful backtraces see https://wiki.gentoo.org/wiki/Project:Quality_Assurance/Backtraces |
hpn | Enable high performance ssh |
kerberos | Add kerberos support |
ldns | Use LDNS for DNSSEC/SSHFP validation. |
libedit | Use the libedit library (replacement for readline) |
libressl | Use dev-libs/libressl instead of dev-libs/openssl when applicable (see also the ssl useflag) |
livecd | Enable root password logins for live-cd environment. |
pam | Add support for PAM (Pluggable Authentication Modules)DANGEROUS to arbitrarily flip |
pie | Build programs as Position Independent Executables (a security hardening technique) |
scp | Enable scp command with known security problems. See bug 733802 |
sctp | Support for Stream Control Transmission Protocol |
security-key | Include builtin U2F/FIDO support |
selinux | !!internal use only!! Security Enhanced Linux support, this must be set by the selinux profile or breakage will occur |
ssl | Enable additional crypto algorithms via OpenSSL |
static | !!do not set this during bootstrap!! Causes binaries to be statically linked instead of dynamically |
test | Enable dependencies and/or preparations necessary to run tests (usually controlled by FEATURES=test but can be toggled independently) |
xmss | Enable XMSS post-quantum authentication algorithm |
Emerge
After changing the necessary USE flags, do not forget to install (or rebuild) OpenSSH:
Configuration
Create keys
In order to provide a secure shell, cryptographic keys are used to manage the encryption, decryption, and hashing functionalities offered by SSH.
On the first start of the SSH service, system keys will be generated. Keys can be (re)generated using the ssh-keygen command.
To generate the keys for SSH protocol version 2 (DSA and RSA algorithms):
root #/usr/bin/ssh-keygen -t dsa -f /etc/ssh/ssh_host_dsa_key -N 'root #/usr/bin/ssh-keygen -t rsa -f /etc/ssh/ssh_host_rsa_key -N 'The article Secure Secure Shell suggests using Ed25519 and RSA public key algorithms with:
root #/usr/bin/ssh-keygen -t ed25519 -a 100 -f /etc/ssh/ssh_host_ed25519_key -N 'root #/usr/bin/ssh-keygen -t rsa -b 4096 -o -a 100 -f /etc/ssh/ssh_host_rsa_key -N 'Server configuration
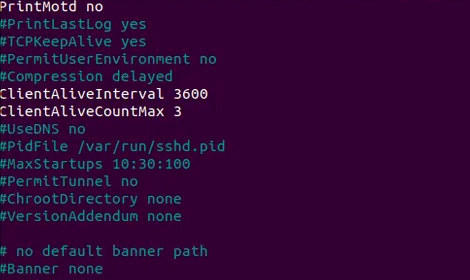
The SSH server is usually configured in the /etc/ssh/sshd_config file, though it is also possible to perform further configuration in OpenRC's /etc/conf.d/sshd, including changing the location of the configuration file. For detailed information on how to configure the server see the sshd_configman page.
Users should study Sven Vermeulen (SwifT)'s OpenSSH guide for a security focused configuration.
The server provides means to validate its configuration using test mode:
Always validate the configuration changes prior restarting the service in order to keep the remote login available.
Client configuration
The ssh client and related programs (scp, sftp, etc.) can be configured using the following files:
- ~/.ssh/config
- /etc/ssh/ssh_config
For more information read the ssh_config manual:
Intrusion prevention
SSH is a commonly attacked service. Tools such as sshguard and fail2ban monitor logs and black list remote users who have repeatedly attempted, yet failed to login. Utilize them as needed to secure a frequently attacked system.
Usage
Running the SSH server
OpenRC
Add the OpenSSH daemon to the default runlevel:
Start the sshd daemon with:
The OpenSSH server can be controlled like any other OpenRC-managed service:
root #rc-service sshd stopActive SSH connections to the server remain unaffected when issuing rc-service sshd restart.
systemd
To have the OpenSSH daemon start when the system starts:
To start the OpenSSH daemon now:
To check if the service has started:
Escape sequences

During an active SSH session, pressing the tilde (~) key starts an escape sequence. Enter the following for a list of options:
Connecting to a distant SSH server
Passwordless authentication
Handy for git server management.
Client
On the client, if not already done, create a key pair. This can be done by running the following command (of course, not entering a passphrase):
Server
Make sure an account for the user exists on the server, and then place the clients' id_rsa.pub file into the server's ~/.ssh/authorized_keys file in the user's home directory. This can be done by running the following command on the client computer (here, the user's passphrase on the server needs to be entered):
Afterwards a passwordless login should be possible doing
Then on the server, the file /etc/ssh/sshd_config should be set to PasswordAuthentication no.
Single machine testing
The above procedure can be tested out locally:
Troubleshooting
There are 3 different levels of debug modes that can help troubleshooting issues. With the -v option SSH prints debugging messages about its progress. This is helpful in debugging connection, authentication, and configuration problems. Multiple -v options increase the verbosity. Maximum verbosity is three levels deep.
user $ssh example.org -vvDeath of long-lived connections
Many internet access devices perform Network Address Translation (NAT), a process that enables devices on a private network such as that typically found in a home or business place to access foreign networks, such as the internet, despite only having a single IP address on that network. Unfortunately, not all NAT devices are created equal, and some of them incorrectly close long-lived, occasional-use TCP connections such as those used by SSH. This is generally observable as a sudden inability to interact with the remote server, even though the ssh client program has not exited.
In order to resolve the issue, OpenSSH clients and servers can be configured to send a 'keep alive', or invisible message aimed at maintaining and confirming the live status of the link:
- To enable keep alive for all clients connecting to your local server, set
ClientAliveInterval 30(or some other value, in seconds) within the /etc/ssh/sshd_config file. - To enable keep alive for all servers connected to by your local client, set
ServerAliveInterval 30(or some other value, in seconds) within the /etc/ssh/ssh_config file.
X11 forwarding, not forwarding, or tunneling
Problem: After having made the necessary changes to the configuration files for permitting X11 forwarding, it is discovered X applications are executing on the server and are not being forwarded to the client.
Solution: What is likely occurring during SSH login into the remote server or host, the DISPLAY variable is either being unset or is being set after the SSH session sets it.
Test for this scenario perform the following after logging in remotely:
The output should be something similar to localhost:10.0 or localhost2.local:10.0 using server side X11UseLocalhost no setting. If the usual :0.0 is not displayed, check to make sure the DISPLAY variable within ~/.bash_profile is not being unset or re-initializing. If it is, remove or comment out any custom initialization of the DISPLAY variable to prevent the code in ~/.bash_profile from executing during a SSH login:
Be sure to substitute larry in the command above with the proper username.
A trick that works to complete this task would be to define an alias within the users' ~/.bashrc file.
ssh-agent
OpenSSH comes with ssh-agent, a daemon to cache and prevent from frequent ssh password entries. When run, the environment variable SSH_AUTH_SOCK is used to point to ssh-agent's communication socket. The normal way to setup ssh-agent is to run it as the top most process of the user's session. Otherwise the environment variables will not be visible inside the session.
Depending on the way the graphical user session is configured to launch, it can be tricky to find a suitable way to launch ssh-agent. As an example for the lightdm display manager, you may edit and change /etc/lightdm/Xsession from
into
To tell ssh-agent the password once per session, either run ssh-add manually or make use of the AddKeysToAgent option.
Recent Xfce[1] will start ssh-agent (and gpg-agent) automatically. If both are installed both will be started which makes identity management especially with SmartCards more complicated. Either stop XFCE from autostarting at least SSH's agent or disable both and use your shell, X-session or similar.
user $xfconf-query -c xfce4-session -p /startup/ssh-agent/enabled -n -t bool -s falseuser $xfconf-query -c xfce4-session -p /startup/gpg-agent/enabled -n -t bool -s falseSee also
- Securing the SSH service (Security Handbook)
- Keychain — This document describes how to use SSH shared keys along with the keychain program.
- Autossh — a command that detects when SSH connections drop and automatically reconnects them.
- SCP — an interactive file transfer program, similar to the copy command, that copies files over an encrypted SSH transport.
- SFTP — an interactive file transfer program, similar to ftp, which performs all operations over an encrypted SSH transport.
- SSHFS — a secure shell client used to mount remote filesystems to local machines.
- dropbear — a lightweight SSH server. It runs on a variety of POSIX-based platforms.
External resources
- net-misc/connect — SSH Proxy Command -- connect.c
- https://lonesysadmin.net/2011/11/08/ssh-escape-sequences-aka-kill-dead-ssh-sessions/amp/ - A blog entry on escape sequences.
- https://hackaday.com/2017/10/18/practical-public-key-cryptography/ - Practical public key cryptography (Hackaday).
This tutorial walks you through creating and connecting to a virtual machine (VM) on Azure using the Visual Studio Code Remote - SSH extension. You'll create a Node.js Express web app to show how you can edit and debug on a remote machine with VS Code just like you could if the source code was local.
Note: Your Linux VM can be hosted anywhere - on your local host, on premise, in Azure, or in any other cloud, as long as the chosen Linux distribution meets these prerequisites.
Prerequisites
To get started, you need to have done the following steps:
- Install an OpenSSH compatible SSH client (PuTTY is not supported).
- Install Visual Studio Code.
- Have an Azure subscription (If you don't have an Azure subscription, create a free account before you begin).
Install the extension
The Remote - SSH extension is used to connect to SSH hosts.
Remote - SSH
With the Remote - SSH extension installed, you will see a new Status bar item at the far left.
The Remote Status bar item can quickly show you in which context VS Code is running (local or remote) and clicking on the item will bring up the Remote - SSH commands.
Create a virtual machine
If you don't have an existing Linux virtual machine, you can create a new VM through the Azure portal. In the Azure portal, search for 'Virtual Machines', and choose Add. From there, you can select your Azure subscription and create a new resource group, if you don't already have one.
Note: In this tutorial, we are using Azure, but your Linux VM can be hosted anywhere, as long as the Linux distribution meets these prerequisites.
Now you can specify details of your VM, such as the name, the size, and the base image. Choose Ubuntu Server 18.04 LTS for this example, but you can choose recent versions of other Linux distros and look at VS Code's supported SSH servers.
Set up SSH
There are several authentication methods into a VM, including an SSH public/private key pair or a username and password. We strongly recommend using key-based authentication (if you use a username/password, you'll be prompted to enter your credentials more than once by the extension). If you're on Windows and have already created keys using PuttyGen, you can reuse them.
Create an SSH key
If you don't have an SSH key pair, open a bash shell or the command line and type in:
This will generate the SSH key. Press Enter at the following prompt to save the key in the default location (under your user directory as a folder named .ssh).
You will then be prompted to enter a secure passphrase, but you can leave that blank. You should now have a id_rsa.pub file which contains your new public SSH key.
Add SSH key to your VM
In the previous step, you generated an SSH key pair. Select Use existing public key in the dropdown for SSH public key source so that you can use the public key you just generated. Take the public key and paste it into your VM setup, by copying the entire contents of the id_rsa.pub in the SSH public key. You also want to allow your VM to accept inbound SSH traffic by selecting Allow selected ports and choosing SSH (22) from the Select inbound ports dropdown list.
Auto shutdown
A cool feature of using Azure VMs is the ability to enable auto shutdown (because let's face it, we all forget to turn off our VMs…). If you go to the Management tab, you can set the time you want to shut down the VM daily.
Select Review and Create, then Create, and Azure will deploy your VM for you!
Once the deployment is finished (it may take several minutes), go to the new resource view for your virtual machine.
Connect using SSH
Now that you've created an SSH host, let's connect to it!
You'll have noticed an indicator on the bottom-left corner of the Status bar. This indicator tells you in which context VS Code is running (local or remote). Click on the indicator to bring up a list of Remote extension commands.
Choose the Remote-SSH: Connect to Host command and connect to the host by entering connection information for your VM in the following format: user@hostname.
The user is the username you set when adding the SSH public key to your VM. For the hostname, go back to the Azure portal and in the Overview pane of the VM you created, copy the Public IP address.
Before connecting in Remote - SSH, you can verify you're able to connect to your VM via a command prompt using ssh user@hostname.
Note: If you run into an error ssh: connect to host <host ip> port 22: Connection timed out, you may need to delete NRMS-Rule-106 from the Networking tab of your VM:
Set the user and hostname in the connection information text box.
VS Code will now open a new window (instance). You'll then see a notification that the 'VS Code Server' is initializing on the SSH Host. Once the VS Code Server is installed on the remote host, it can run extensions and talk to your local instance of VS Code.
You'll know you're connected to your VM by looking at the indicator in the Status bar. It shows the hostname of your VM.
The Remote - SSH extension also contributes a new icon on your Activity bar, and clicking on it will open the Remote explorer. From the dropdown, select SSH Targets, where you can configure your SSH connections. For instance, you can save the hosts you connect to the most and access them from here instead of entering the user and hostname.
Once you're connected to your SSH host, you can interact with files and open folders on the remote machine. If you open the integrated terminal (⌃` (Windows, Linux Ctrl+`)), you'll see you're working inside a bash shell while you're on Windows.
You can use the bash shell to browse the file system on the VM. You can also browse and open folders on the remote home directory with File > Open Folder.
Create your Node.js application
In this step, you will create a simple Node.js application. You will use an application generator to quickly scaffold out the application from a terminal.
Install Node.js and npm
From the integrated terminal (⌃` (Windows, Linux Ctrl+`)), update the packages in your Linux VM, then install Node.js, which includes npm, the Node.js package manager.
You can verify the installations by running:
Install the Express generator
Express is a popular framework for building and running Node.js applications. You can scaffold (create) a new Express application using the Express Generator tool. The Express Generator is shipped as an npm module and installed by using the npm command-line tool npm.
Ssh Openssh
The -g switch installs the Express Generator globally on your machine so that you can run it from anywhere.
Create a new application
You can now create a new Express application called myExpressApp by running:
The --view pug parameters tell the generator to use the pug template engine.
To install all of the application's dependencies, go to the new folder and run npm install.
Run the application
Last, let's ensure that the application runs. From the terminal, start the application using the npm start command to start the server.
The Express app by default runs on http://localhost:3000. You won't see anything in your local browser on localhost:3000 because the web app is running on your virtual machine.
Port forwarding
To be able to browse to the web app on your local machine, you can leverage another feature called Port forwarding.
To be able to access a port on the remote machine that may not be publicly exposed, you need to establish a connection or a tunnel between a port on your local machine and the server. With the app still running, open the SSH Explorer and find the Forwarded Ports view. Click on the Forward a port link and indicate that you want to forward port 3000:
Name the connection 'browser':
The server will now forward traffic on port 3000 to your local machine. When you browse to http://localhost:3000, you see the running web app.

Edit and debug
From the Visual Studio Code File Explorer (⇧⌘E (Windows, Linux Ctrl+Shift+E)), navigate to your new myExpressApp folder and double-click the app.js file to open it in the editor.
IntelliSense
You have syntax highlighting for the JavaScript file as well as IntelliSense with hovers, just like you would see if the source code was on your local machine.
When you start typing, you'll get smart completions for the object methods and properties.
Debugging
Ubuntu Wiki SSHpage.
Set a breakpoint on line 10 of app.js by clicking in the gutter to the left of the line number or by putting the cursor on the line and pressing F9. The breakpoint will be displayed as a red circle.
Now, press F5 to run your application. If you are asked how to run the application, choose Node.js.
The app will start, and you'll hit the breakpoint. You can inspect variables, create watches, and navigate the call stack.
Press F10 to step or F5 again to finish your debugging session.
You get the full development experience of Visual Studio Code connected over SSH.
Ssh/openssh/keys
Ending your SSH connection
You can end your session over SSH and go back to running VS Code locally with File > Close Remote Connection.
Ssh Openssh 7.6p1 Exploit
Congratulations!
Openssh Ssh Client
Congratulations, you've successfully completed this tutorial!
Next, check out the other Remote Development extensions.
Or get them all by installing the Remote Development Extension Pack.
